Our goal is to make your online interaction with TEACHERPH as valuable as possible, delivering information that is relevant to your needs. We understand many people have concerns about the security of their information, especially when providing their information via the Internet. We are committed to protecting the information you provide us online in the same way we protect all our customer information. We take the privacy of customer data very seriously at TEACHERPH as you can see in our privacy commitment.
Your information is not automatically accessible via the Internet. Once you request online access to your information, we request specific information about you to confirm your identity. We then use several security measures to confirm this information and only then do we allow online access to your information.
When making purchases via our website, your credit card information is safe and secured. Reliable and trusted service providers who specialize in processing online payments handle all credit card transactions on our behalf.
How We Protect Your Information Online
On our website, we use a combination of Secure Socket Layer (SSL) encryption, Web Application Firewall (WAF), Open Web Application Security Project (OWASP), Multi-Factor Authentications, Denial-of-Service (DDoS) mitigation, and Timed Logouts to ensure confidentiality. The following explains the technologies used to secure your information.
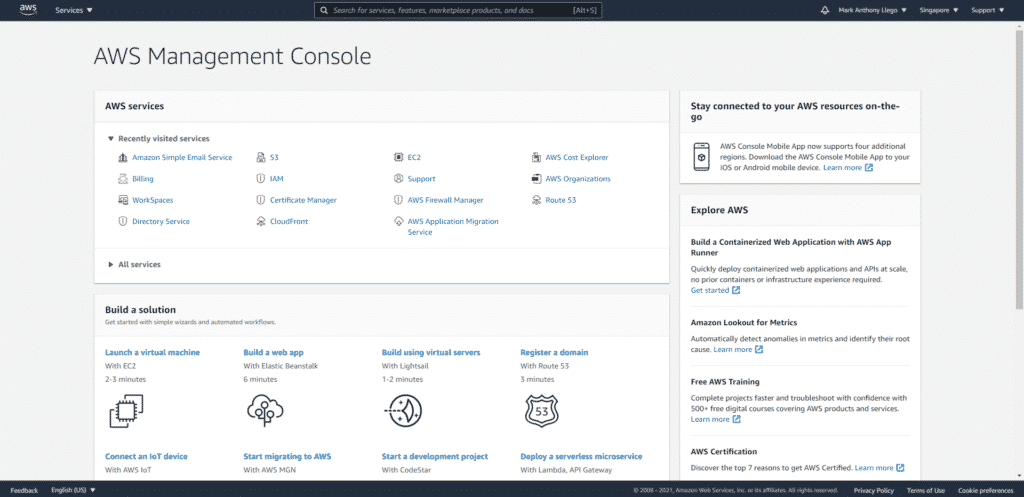
TeacherPH Infrastructure
The infrastructure and associated security are provided by Amazon Web Services (AWS). All data is hosted on Amazon’s data center located in Singapore and Seoul.
The hosting service is provided in a safe ’limited access’ environment. There is a continuous supply of power, climate control, and the data center is protected against natural disasters. In the unlikely event that a situation occurs where it will be reasonable to question the data center’s security the customer can request an independent 3rd party to examine the security systems at the customers’ cost if the customer compensates Cookie Information for all costs which Cookie Information may experience as a direct consequence hereof including costs to be paid to the data center for access. Access to the data centers’ infrastructure is decided in full by the data center. Access to the data center is limited to specific employees and selected production/support specialists who are only allowed access to perform planned maintenance and upgrades.
TEACHERPH reserves the right to change the data center and/or other suppliers without obtaining prior consent from the customer, provided that the new data center or new other supplier provides the Customer with at least the same service level and security as the current.
For more info, visit the Amazon AWS page.
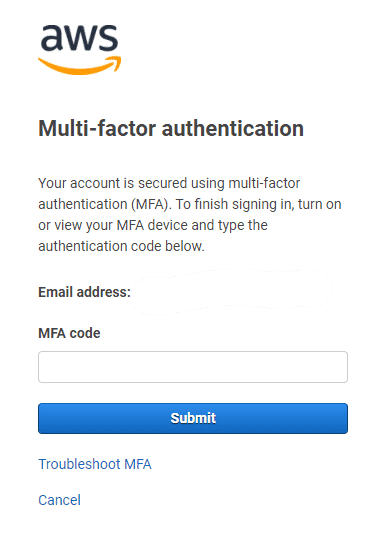
Identity and Access Management
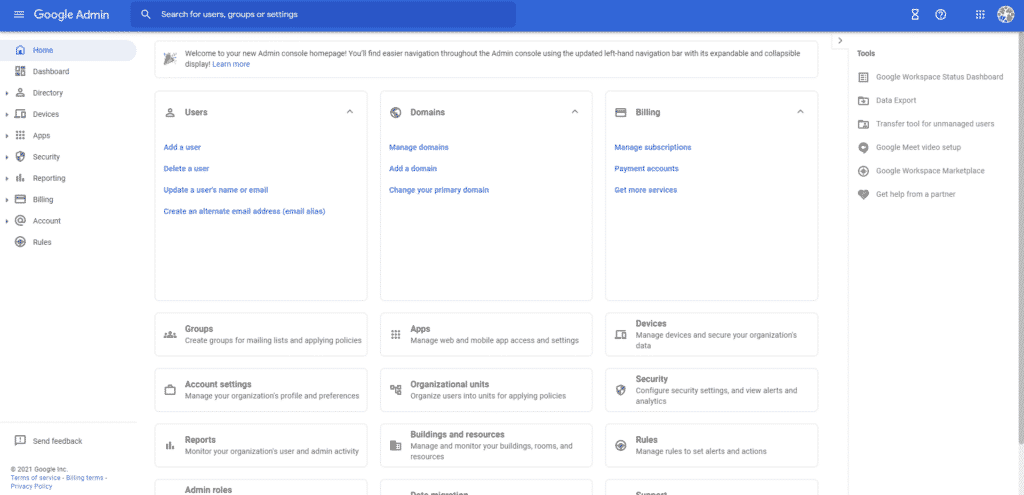
TEACHERPH uses an effective implementation that includes configuration of administrative services, establishing and configuration of user identities, and implementation of service- and role-based access controls. Furthermore, we are monitoring, controlling, and logging both users and end-points.
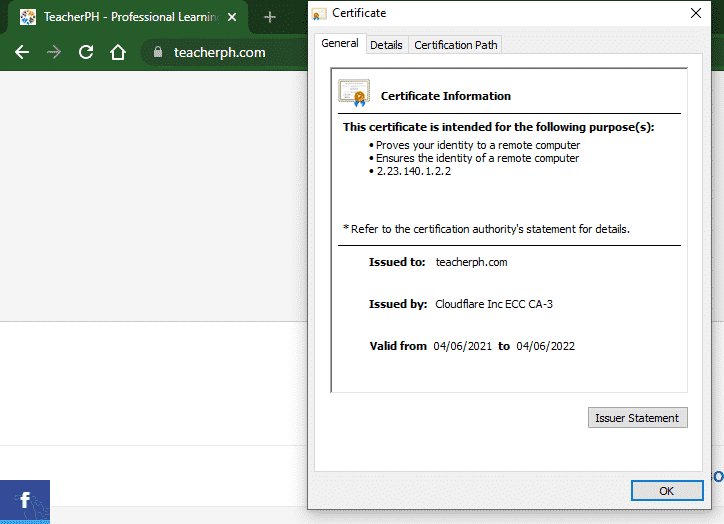
The Secure Socket Layer (SSL)
SSL is an industry-standard protocol used for communication between your Web browser and our Web servers. It provides authentication, data integrity, and encryption.
Your browser may give you a message indicating you are entering a secure website. You may also see a green lock outlining the secure page. And if you usually see a broken key or open lock in the lower-left corner of your screen, you’ll notice it change to a full key or closed lock.
Secured transactions are also indicated in the location or address bar of your browser by the prefix https:// rather than http:// (https stands for hyper-text transfer protocol, secured).
Email Security
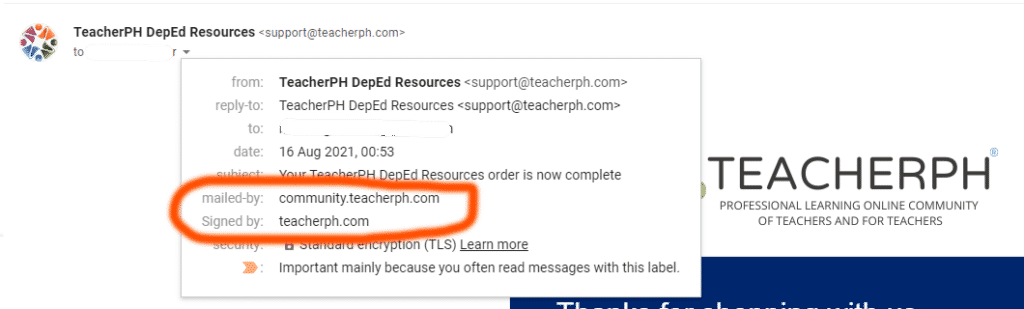
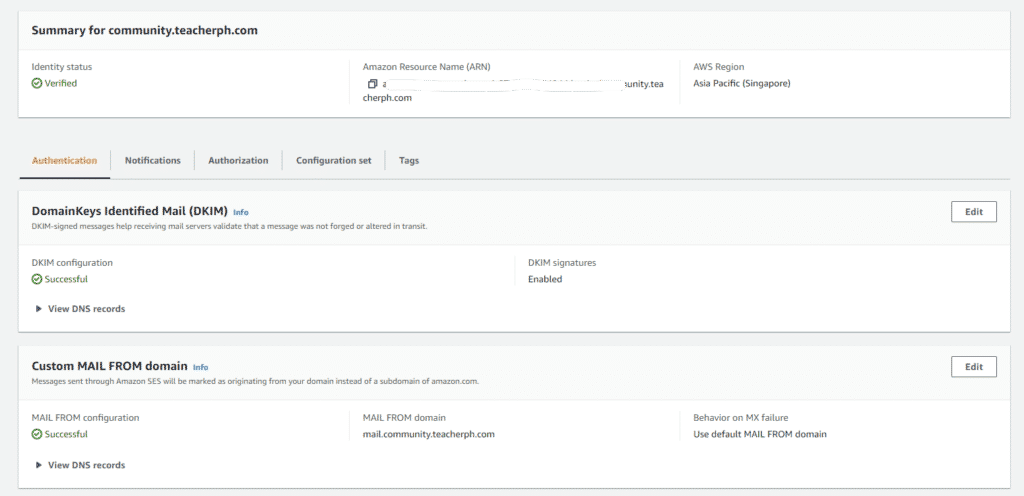
TeacherPH uses DomainKeys Identified Mail (DKIM) standard to help us prevent spoofing on outgoing messages sent from our servers.
DKIM adds an encrypted signature to the header of all outgoing messages. Email servers that get signed messages use DKIM to decrypt the message header and verify the message was not changed after it was sent.
In addition to DKIM, TeacherPH uses Sender Policy Framework (SPF) and Domain-based Message Authentication, Reporting & Conformance (DMARC).
- Sender Policy Framework (SPF) – SPF specifies which TeacherPH domains can send messages for our organization.
- Domain-based Message Authentication, Reporting & Conformance (DMARC) – DMARC specifies how our domain handles suspicious emails.
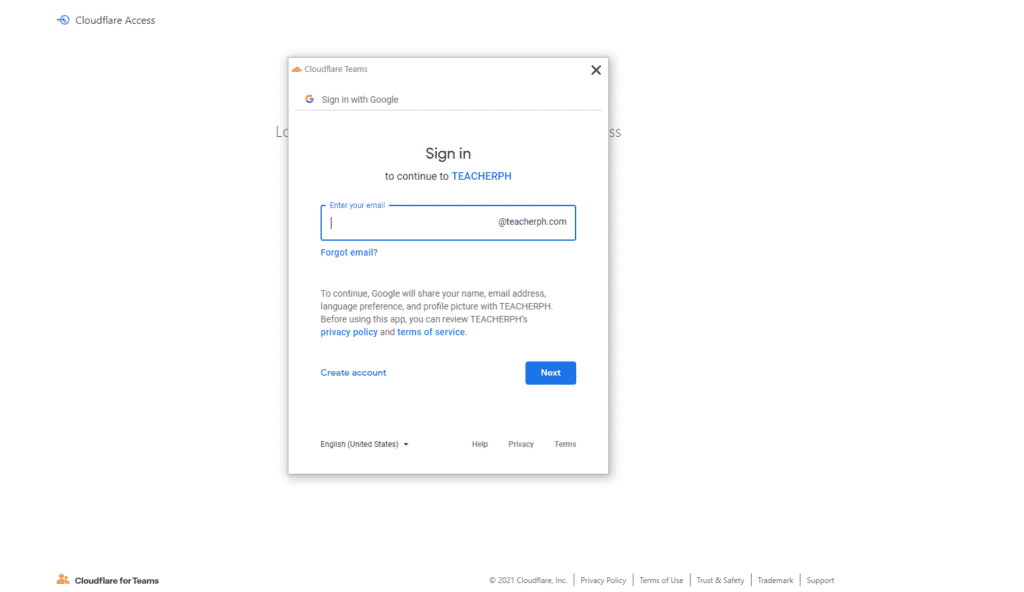
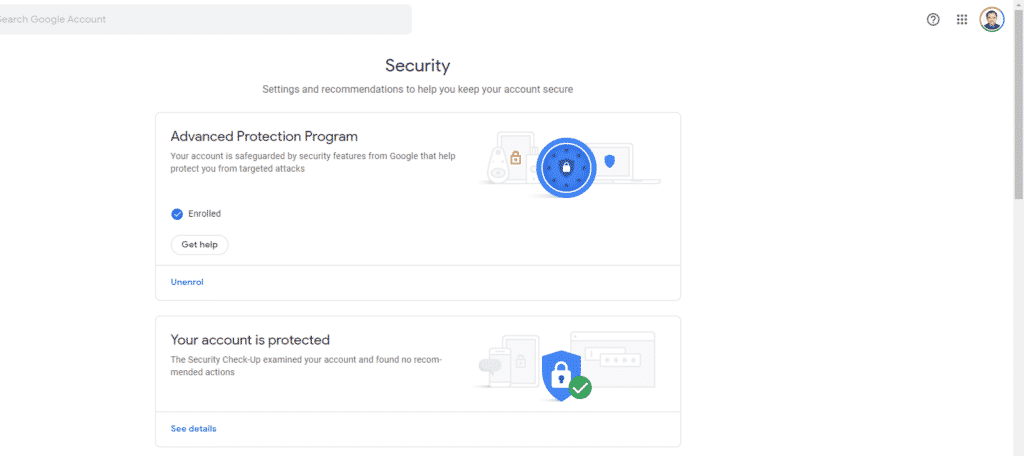
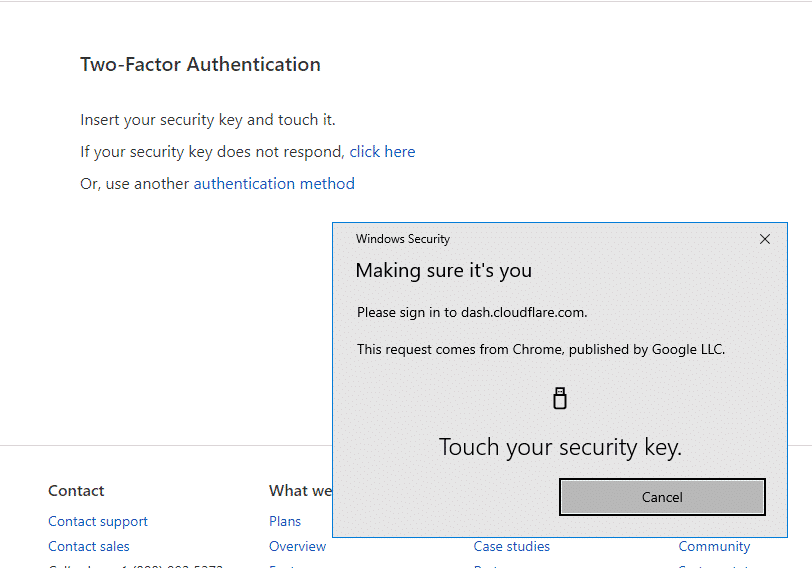
Authentication
Authentication confirms that you are who you say you are and verifies that you are communicating with a TeacherPH Web server. There are two parts to the authentication process, digital certificates as well as your identification and password.
The Secure Socket Layer uses digital certificates to confirm with your Web browser that you are accessing our Web server. Our website uses Cloudflare digital certificates, the strongest security available for websites. Digital certificates let you verify whom you are dealing with. Our certificate allows you to confirm that you are dealing with TEACHERPH and that we own the website to which you are connected.
You can check the digital certificate for our website to establish that you have a secure connection by simply clicking on the padlock seal whenever you see it appear on our site.
Some of our services require you to have a personal digital ID certificate installed on your computer. We provide specific instructions for installing this personal digital ID only when it is required by our systems. For most of the services we provide on our website, this personal digital ID is not required.
Your user ID, or group and ID numbers as well as your password are confirmed to ensure your information is provided only to the correct identification and corresponding password. Incorrect identification and/or password will result in failure to access your information.
Data Integrity
Data at rest is encrypted and decrypted using 256-bit AES encryption, one of the strongest block ciphers available, and is FIPS 140-2 compliant.
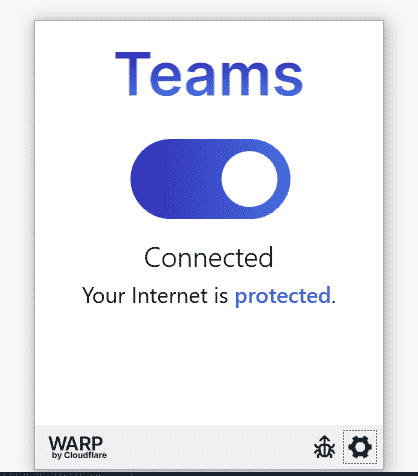
The web-based application uses secure HTTP (TLS/HTTPS) to protect data transmissions over the internet. Virtual Private Network (VPN) technology is used to protect other transmissions such as access to the active database.
Encryption
The Secure Socket Layer encrypts or “scrambles” the content we transmit into an unreadable format using complex mathematical equations, called algorithms before it travels across the Internet to your Web browser. This makes it difficult for unauthorized interceptors to understand. Encryption codes the information ensuring that only your Web browser and our Web server can decode it effectively.
Your Web browser will display a closed padlock icon when data is encrypted. An open lock or no image is displayed during an unencrypted session.
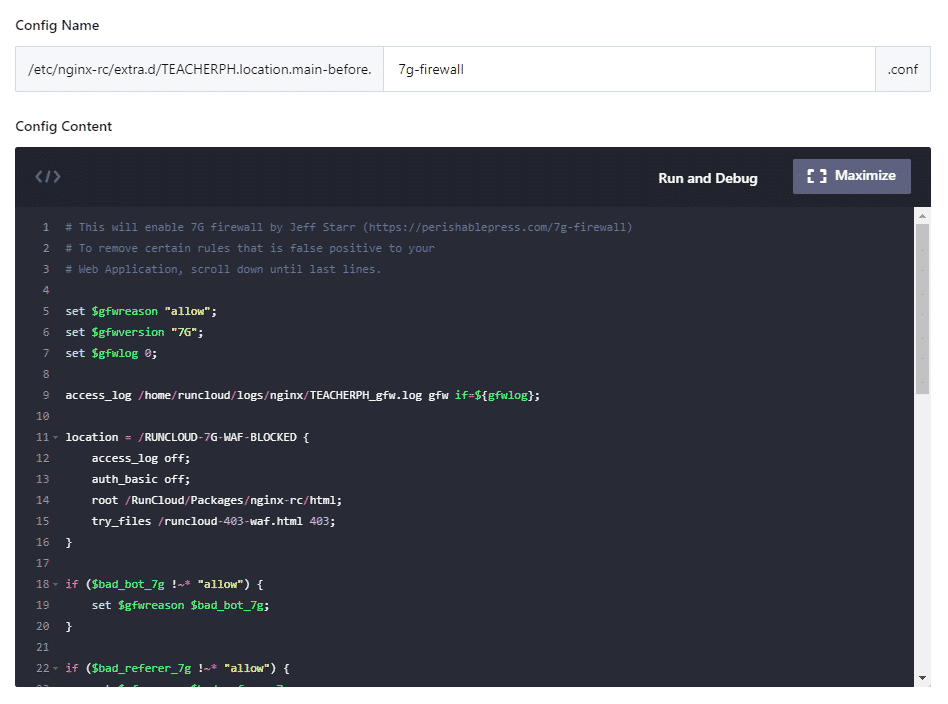
Firewall
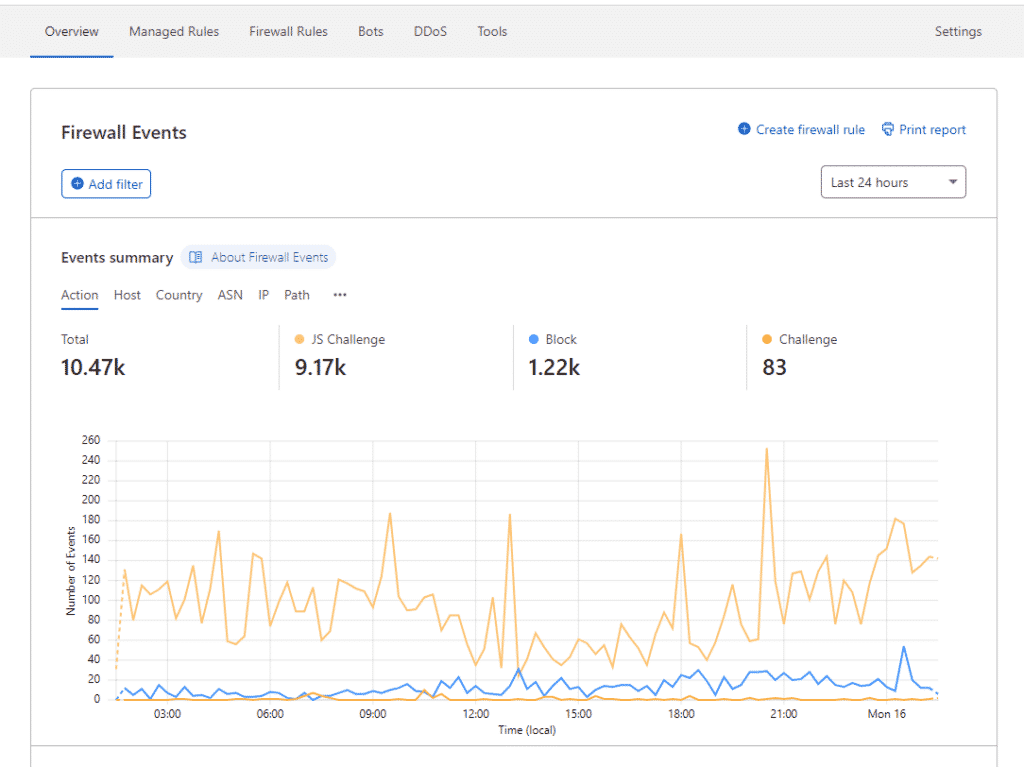
Our systems are protected by firewalls that are a combination of the latest in computer hardware and software to separate the Internet from TeacherPH Web servers and computer systems. The purpose of a firewall is to prevent unauthorized access and malicious attacks to customer information and business systems. By using a firewall, TeacherPH is ensuring your information is always protected.
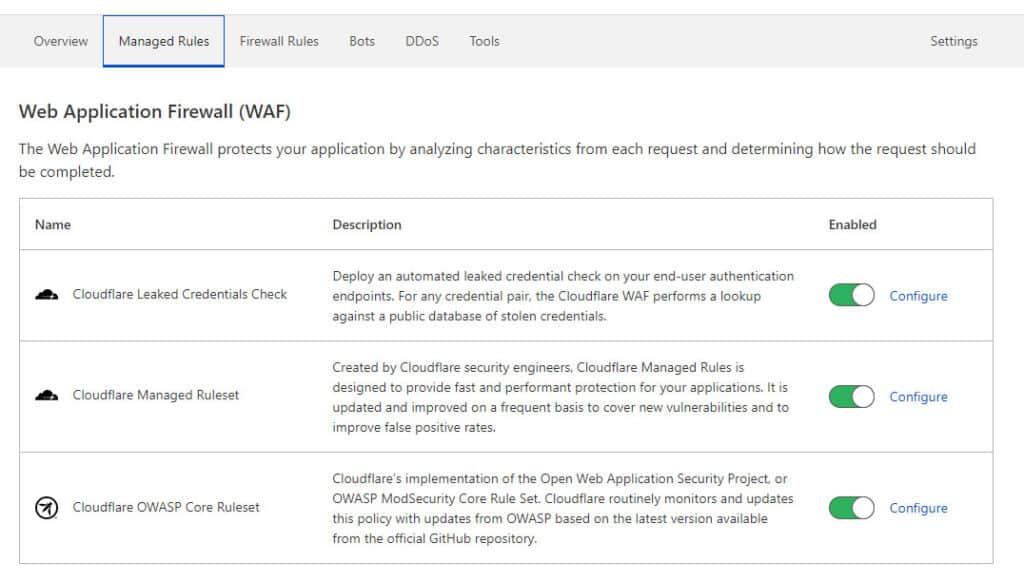
A Web Application Firewall (WAF) is an application firewall for HTTP applications. It applies a set of rules to an HTTP conversation. Generally, these rules cover common attacks such as cross-site scripting (XSS) and SQL injection.
The Open Web Application Security Project is an online community that creates freely available articles, methodologies, documentation, tools, and technologies in the field of web application security.
Multi-Factor Authentication is an extra layer of security that requires not only a password and username but also something that the user has on them.
DDoS mitigation is a set of techniques or tools for resisting or mitigating the impact of distributed denial-of-service (DDoS) attacks on networks attached to the Internet by protecting the target and relay networks. DDoS attacks are a constant threat to businesses and organizations by threatening service performance or shutting down a website entirely, even for a short time.
Timed Sign Outs
Our Web services are time-sensitive in that an online session will be terminated after a certain period of inactivity. This is a security measure to help prevent unauthorized access to our systems if an individual leaves their computer unattended for an extended period of time while connected to our website.
Backups
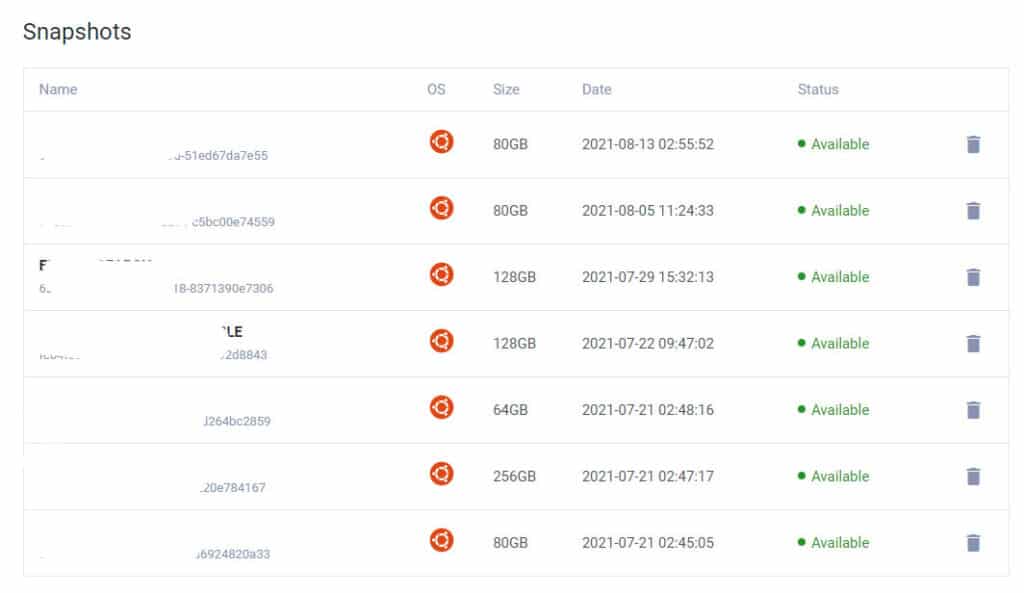
TEACHERPH provides web servers, application servers, database servers, and physical storage in which data is kept in a redundant multi-drive configuration which gives mirrored storage and the required software to host the solution and associated services.
Additionally, all critical data is backed up daily to encrypted, geo-redundant storage.
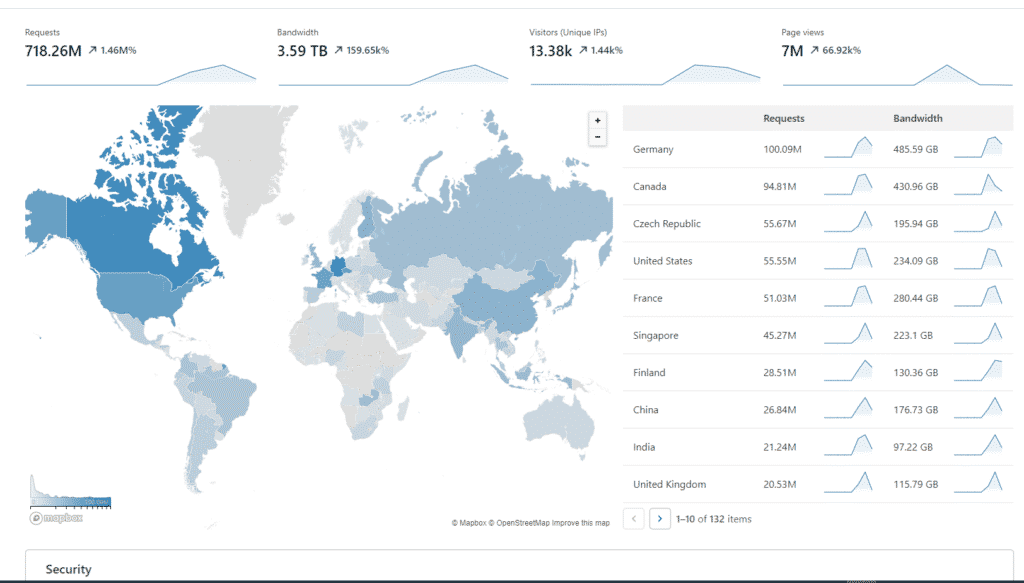
Availability
TEACHERPH will provide the required infrastructure to ensure that the solution is available via the internet 99,5% of the time measured per month from the go-live date.
The service takes advantage of the wide opportunities in Amazon AWS to ensure high availability including full redundancy for all components and services, load balancing, automatic scaling of capacity, self-healing components, and a traffic manager to automatic geographic failover in case of an emergency at the data center level.
All server, middleware, and application components are being monitored 24/7 by TEACHERPH.
If you have any additional questions or concerns related to these security practices, please email us at support@teacherph.com or use our contact form.